| Status | ||||
|---|---|---|---|---|
|
...
Add Redirect URLs for your Picturepark
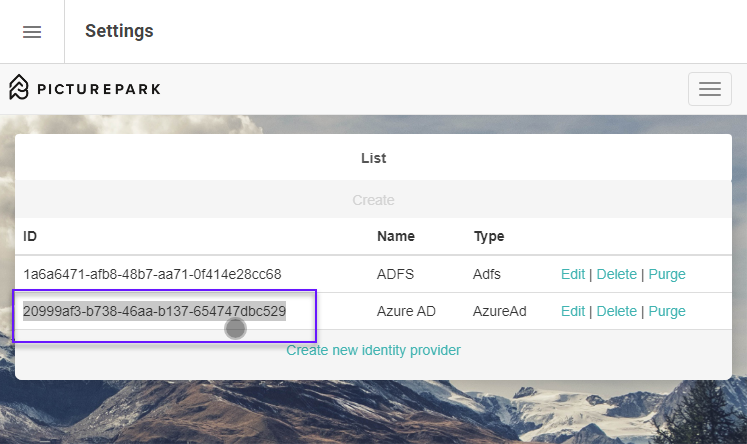
Code Block https://ids-cp-ch.picturepark.com/signin-<idpid> (e.g.https://ids-cp-ch.picturepark.com/signin-bb09dece-aeb5-47fb-8be5-30504e2ba9dc)
The ID is the one from Picturepark when creating a new Identity Provider.
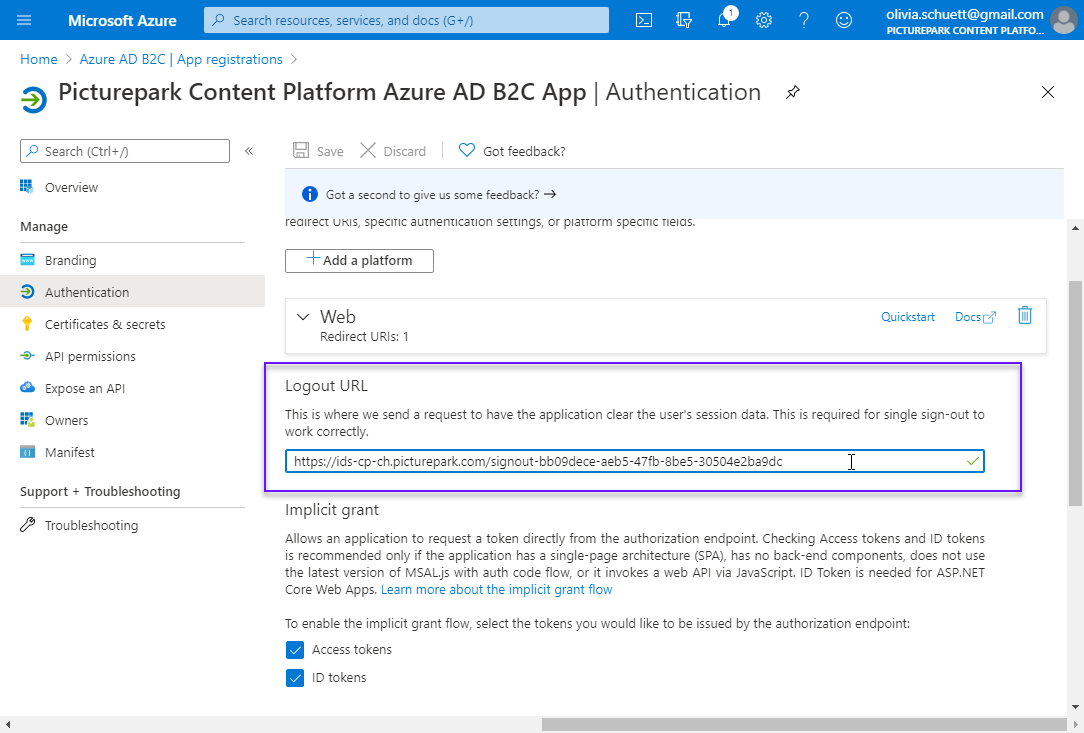
Add a Logout URL if you would like one. This is optional and is not required for authentication to work. It is a convenience if users are logging out of the Azure AD, this will then log them out of picturepark IDS and within 10 minutes at the latest Picturepark itself.
Code Block https://ids-cp-ch.picturepark.com/signout-<idpid> (e.g.https://ids-cp-ch.picturepark.com/signout-bb09dece-aeb5-47fb-8be5-30504e2ba9dc)
Implicit grant
Leave this empty, don't select anything.
Picturepark Open ID Connect integration uses code flow, not implicit flow.
Advanced settings
Treat application as a public client. → YES
Add API Permissions
Add permission
Select Microsoft Graph
Select Delegated permissions
Select and save
email
offline_access
openid
profile
...
Open Manage > Expose an API
Add a scope
You'll need to set an Application ID URI before you can add permission. (Microsoft chooses one by default but it can be changed). Save and continue
Scope name: user.signin
Who can consent? Admins only
Consent display names: User Authentication
Consent descriptions: User Authentication
Click Add scope
Add a new client application
Client ID is taken from the Overview page
Select Scopes
...